Frenkey

Smart Access Control
Open your doors by the smartphone. Frenkey is a smart access control service that turns your smartphone in a key ring. Frenkey APP controls and checks your locks from anywhere. Opening a door is super simple: select the key from the app, authenticate with biometrics or a PIN, and the door opens. It's that easy! Moreover Frenkey app allows to create a digital key, deliver it online, check log of access, administer the keys: enable, disable and destroy the keys. Frenkey evolves access experience and makes locks smart (Smart Lock).
Frenkey is especially designed for hauses, companies, condominiums, B&Bs, hotels, offices, studios, or anywhere need to unlock a lock, door, or entrance. No keys, cards, or remote controls are needed. You need only the smartphone with Frenkey App.
Evolve Access Experience
Frenkey provides an evolutionary access experience with keyless access control. A simple user interface organizes digital keys in digital key chains. Keys can be created, delivered to users and destroyed easily and securely just by a mobile phone and online without the need of any physical interaction. Each user can control several keys of different smart locks installed at different locations.

Frenkey Box
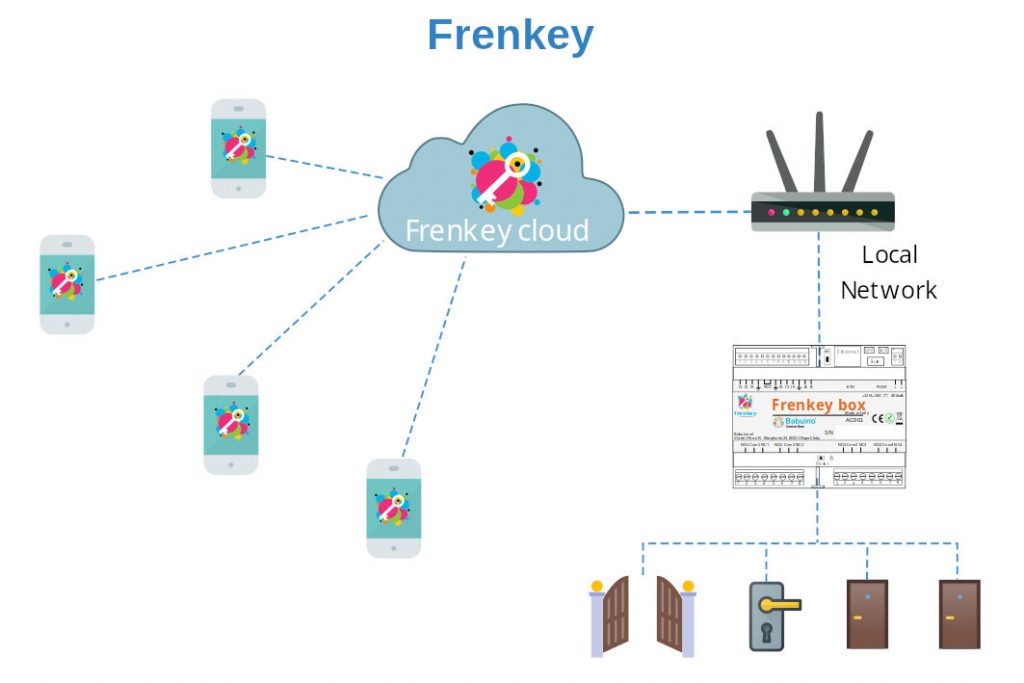
Frenkey Box is the electronic device that makes locks smart and ensures access control security. The system identifies the user with each transaction, allowing access only to the key owner.
Each Frenkey Box unit can control up to four locks. The system is easily expandable by connecting multiple Frenkey Boxes together. There is no need to replace an electric lock as the system is compatible with most existing electric and motorized locks on the market.
Administration
Administration
Frenkey is a cloud-based access control service. Users can securely interact with the smart lock from anywhere. The communication is protected by a secure tunnel that ensures data confidentiality and integrity. The security is end-to-end, meaning that only authorized users can communicate with the device.
Features
-
Management of keys via applet. Keys can be created, distributed, activated, deactivated and destroyed without any physical action on the device.
-
User authentication at each access point by means of biometry or pin.
-
Distribution of keys over the network. Keys can be exchanged securely over the Internet.
-
End to end security.
-
Log of access.
Benefits
For more information Contact Us
